
My colleague Jan Durnhofer wrote an article about how to secure your DCIM solution from security attacks (click here to read it). Continuing the discussion around DCIM and security, I’d like to discuss another key aspect of security for your data center: how DCIM can help managers secure the data center from within the organization.
As you are aware, Data Center Managers today must adhere to the strictest security compliance regulations while also ensuring that their technicians and contractors have proper access to maintain a data center’s availability, assets, costs, and mean-time-to-repair.
Data Center Managers can use Data Center Infrastructure Management (DCIM), to help assist with securing the data center from both external and internal threats.With DCIM, data center teams can not only manage the data center assets, the cabling, and power, but also adhere to security compliance and reduce the security risks.
Here are some of the ways you can secure your data center assets using DCIM software:
Role-Based Permissions
Some of the biggest threats are the ones that can come internally, from within an organization! Protecting data from getting into the wrong hands (for example, a disgruntled ex-employee) is part of properly securing a data center. Limit your employees’ access to your data center location, and rooms and what they can do in your DCIM solution.To truly protect data, managers need to be able to control the level of access (and set the appropriate roles to its users and groups that have access to data in their data center(s)).
Granular, role-based access permissions in netTerrain DCIM software can help you protect your data centers against internal staff and employees! With netTerrain DCIM, it provides eight roles that you can assign users and groups. Simply check what diagrams your employees can see, not see, or edit.
netTerrain also integrates with existing Active Directory for an additional level of authentication so only authorized users have access to your data center data. Follow regulatory policies and procedures — with role-based permission levels in DCIM software.
Auditing Reports
Along with role-based permissions, tracking each users’ changes is easy with netTerrain DCIM’s Audit Trail and accompanying Dashboard Reports. The audit trail shows a history of who changed what and when. After or during a security breach, you can use these reports to see who has accessed different areas or devices in your data center to understand how this happened and how to prevent future events.
Audit trail actions include:
- All Deletes: To see all the deletes performed within the time frame selected.
- All Inserts: View of all the inserts performed within the time frame selected.
- All Updates: View of all updates performed within the time frame.
- Complete Audit Trail: View of all Deletes, Inserts and Updates within the time frame selected.
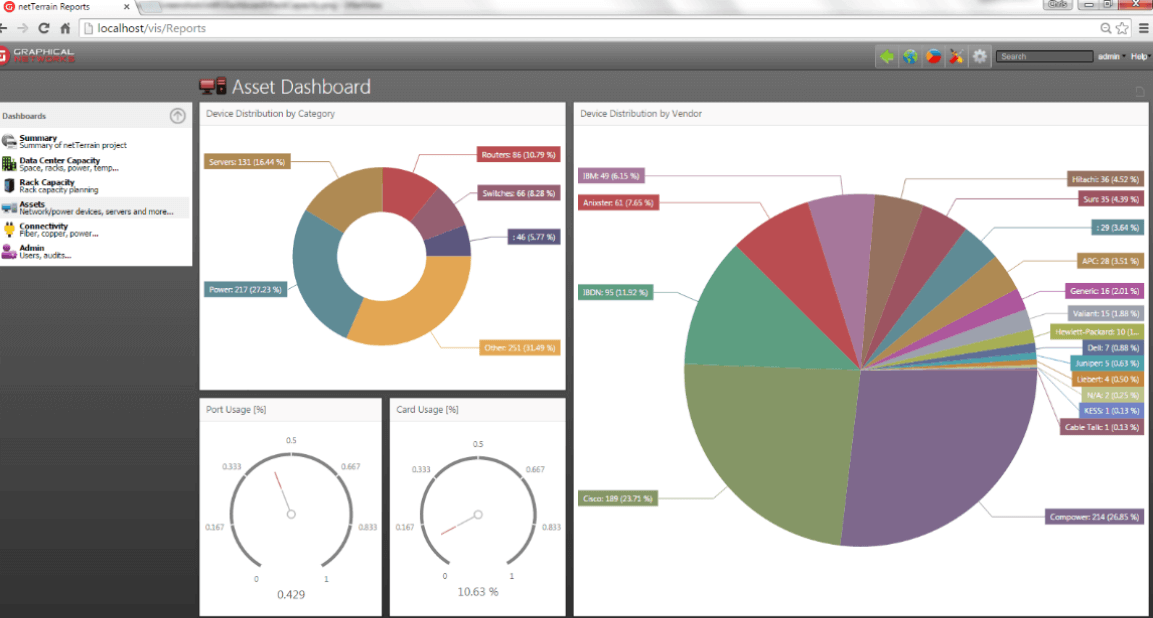 Example of a dashboard report in DCIM software
Example of a dashboard report in DCIM software
Asset Management
You can’t manage what you don’t know — with the right DCIM software, you can know where all of your data center assets are.
netTerrain DCIM software, for example, can track and record the assets in the database and can be used to check the number of installed servers, the software versions in each server via WMI, and includes a SNMP network discovery to discover your assets. Utilize its reporting solutions to see what devices need to be decommissioned, if servers have old versions of software, and detect any unwanted devices (USB sticks, etc.) that are in the data center.
 Example of a physical floorplan in DCIM software
Example of a physical floorplan in DCIM software
Physical Security Cameras
Another key aspect to security is the physical data center room (and/or buildings). Most data centers have surveillance cameras to monitor the physical security of data centers. In addition to network cameras, video management and recording platforms, and intelligent access control hardware and software have enhanced the possibility of securing the data center further.
With netTerrain DCIM, you can view your IP security cameras and view it on a standard HTML 5 web browser. You can centralize your security through netTerrain and view your data center cameras – or the surrounding areas. Some of our netTerrain customers even document the cameras on a university parking lot!
To sum up: the goal of data center security is to allow authorized users in while keeping intruders out, both physically and in relation to cyberattacks. netTerrain DCIM can help Data Center Managers in their quest to secure its Data Centers against external and internal threats.
